
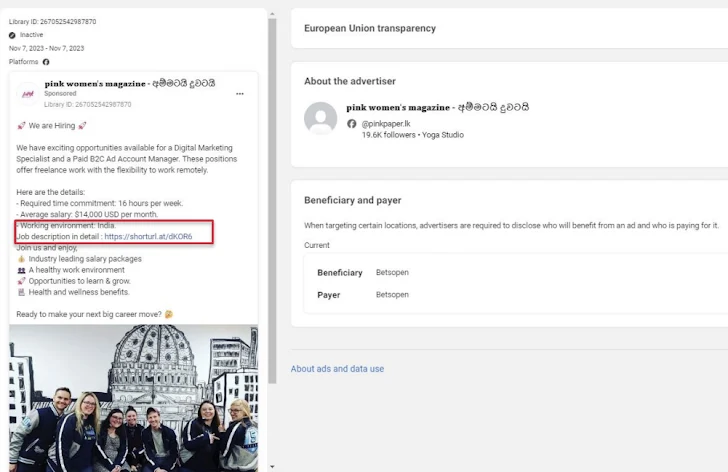
Threat actors are using fake job ads on Facebook as bait to trick potential targets into installing a new code-named Windows-based stealer malware Ov3r_Stealer.
“This malware is designed to steal credentials and crypto wallets and send them to a Telegram channel monitored by the threat actor,” Trustwave SpiderLabs said in a report shared with The Hacker News.
Ov3r_Stealer is capable of stealing location based on IP address, hardware information, passwords, cookies, credit card information, autofills, browser extensions, crypto wallets, Microsoft Office documents and a list of antivirus products installed on the ‘host compromised.
While the exact end goal of the campaign is unknown, it is likely that the stolen information will be offered for sale to other threat actors. Another possibility is that Ov3r_Stealer could be updated over time to act as a QakBot-like loader for additional payloads, including ransomware.

The attack’s starting point is a weaponized PDF file that purports to be a file hosted on OneDrive, prompting users to click an “Access Document” button embedded in it.
Trustwave said it identified the PDF file being shared on a fake Facebook account impersonating Amazon CEO Andy Jassy, as well as through Facebook ads for digital advertising jobs.
Users who end up clicking the button are served an Internet link file (.URL) disguised as a DocuSign document hosted on Discord’s content delivery network (CDN). The shortcut file then serves as a conduit to provide a Control Panel Items (.CPL) file, which is then executed using the Windows Control Panel process binary file (“control.exe”).
Running the CPL file leads to retrieving a PowerShell loader (“DATA1.txt”) from a GitHub repository to finally launch Ov3r_Stealer.
It’s worth noting at this point that Trend Micro recently revealed that a nearly identical infection chain was used by threat actors to take out another rogue called Phmedrone Stealer by exploiting Microsoft Windows Defender’s SmartScreen bypass flaw (CVE-2023- 36025, CVSS Score: 8.8).
The similarities extend to the GitHub repository used (nateeintanan2527) and the fact that Ov3r_Stealer shares code-level overlaps with Phemedrone.
“This malware was reported recently and it may be that Phemedrone has been repurposed and renamed Ov3r_Stealer,” Trustwave said. “The main difference between the two is that Phemedrone is written in C#.”

The findings come as Hudson Rock revealed that threat actors are advertising their access to the law enforcement request portals of major organizations such as Binance, Google, Meta, and TikTok by leveraging credentials obtained from infostealer infections.
They also follow the emergence of a category of infections called CrackedCantil that leverages cracked software as an initial entry vector to release loaders such as PrivateLoader and SmokeLoader, then acting as a delivery mechanism for information thieves, crypto miners, proxy botnets and ransomware.