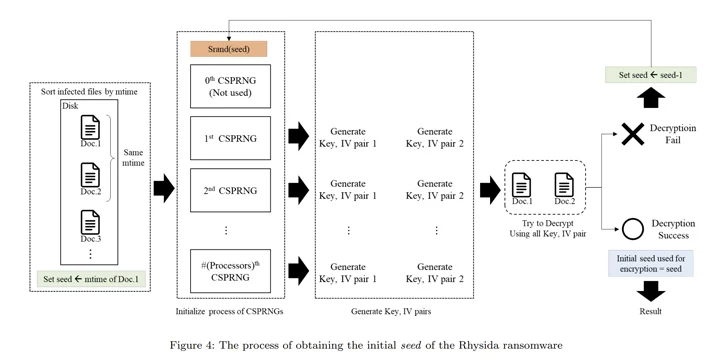
Cybersecurity researchers discovered an “implementation vulnerability” that made it possible to reconstruct encryption keys and decrypt data locked by the Rhysida ransomware.
The findings were published last week by a team of researchers from Kookmin University and the Korea Internet and Security Agency (KISA).
“Through a comprehensive analysis of Rhysida Ransomware, we identified an implementation vulnerability, which allows us to regenerate the encryption key used by the malware,” the researchers said.
The development marks the first successful decryption of the ransomware strain, which first appeared in May 2023. A recovery tool is being distributed via KISA.

The studio is also the latest to achieve data decryption by exploiting ransomware deployment vulnerabilities, following Magniber v2, Ragnar Locker, Avaddon, and Hive.
Rhysida, known to share overlap with another ransomware outfit called Vice Society, uses a tactic known as double extortion to pressure victims into paying by threatening to release their stolen data.
An advisory published by the US government in November 2023 denounced threat actors for staging opportunistic attacks against education, manufacturing, information technology, and government sectors.
An in-depth examination of the inner workings of the ransomware revealed the use of LibTomCrypt for encryption and parallel processing to speed up the process. It has also been found to implement intermittent encryption (also known as partial encryption) to evade detection by security solutions.
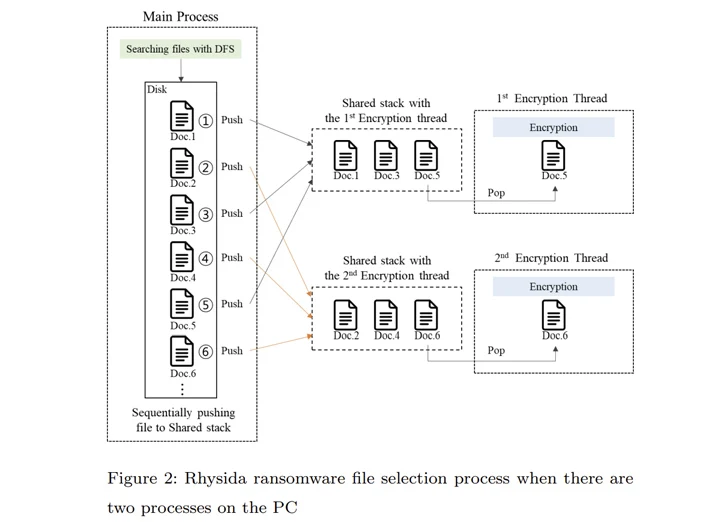
“Rhysida ransomware uses a cryptographically secure pseudo-random number generator (CSPRNG) to generate the encryption key,” the researchers said. “This generator uses a cryptographically secure algorithm to generate random numbers.”
Specifically, the CSPRNG is based on the ChaCha20 algorithm provided by the LibTomCrypt library, with the generated random number also relating to the time the Rhysida ransomware is running.

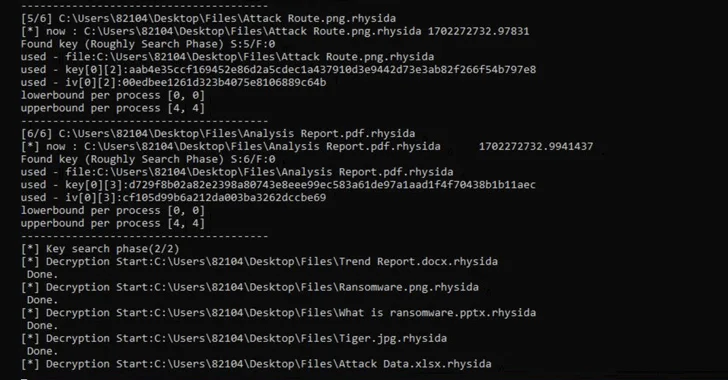
It’s not all. The main process of Rhysida ransomware compiles a list of files to encrypt. This list is subsequently referenced by various threads created to simultaneously encrypt files in a specific order.
“In the encryption process of Rhysida ransomware, the encryption thread generates 80 bytes of random numbers when encrypting a single file,” the researchers noted. “Of these, the first 48 bytes are used as the encryption key and the [initialization vector].”
Using these observations as reference points, the researchers said they were able to recover the initial seed to decrypt the ransomware, determine the “randomized” order in which the files were encrypted, and ultimately recover the data without having to pay a ransom.
“Although these studies are limited in scope, it is important to recognize that some ransomware […] can be successfully deciphered,” the researchers concluded.